Access Security

UniView
Intercom

Hikvision
Intercom

Sewosy
Electromagnets

Conas
Electromagnets
Conas
Access Control

Hikvision
Access Control

Sewosy
Access Control

Jablotron
Access Control
Why an access control system?
The term 'Access Control' usually refers to a system that can control and monitor the movement of people and/or goods into/out of a building or site. The benefits of using access security systems include the prevention of loss or damage to capital assets and the reduced risk of personal injury to staff and visitors. Access security applications range from controlling an entrance door to managing a large complex site. A physical access control system consists of three main components:
1. Access control through the physical barrier
The physical barrier prevents the access of unauthorized persons and has a means of providing access to electrical. These can be: a door equipped with an electromagnet, electric strike, a bolt lock, a parking gate or an elevator. For doors, a magnetic door sensor can be added to monitor the door so that an alarm can be raised if the door is open or illegally opened. Because there is no way to guarantee that only one person will go through a door when it is unlocked, strict rules must be put in place to deter authorized users from allowing unauthorized access through the door
2. Access control by the access controller and reader
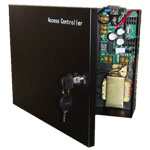
The physical barrier is electronically controlled by a access controller in combination with a form of reader to identify people by their 'credentials' This can be a keypad, a card reader or a biometric reader Together the access controller and reader are able to identify an individual and authorize or open the door for them. controllers can be either 'stand-alone' or networked to a master PC-based (also known as 'on-line') access control system that manages the user database for all access points.The PC-based system software can connect each controller with the details of each individual's access rights.PC-based access control systems can provide many additional facilities such as user location, presence and use monitoring, management and visitor access automatically and of doors during emergencies and assigned periods.
3. Access control by the Credentials
An individual's identity is determined by a 'reference', which can be a PIN code, an access card, key fob or a unique human characteristic, such as a fingerprint. In some cases, combinations of two or more of these credentials can be used to identify the person for an access control system.



